
AI Voice Scams: How To Spot And Stop Them
Voice cloning makes urgent calls harder to trust. Verification habits are now more important than voice recognition.

Voice cloning makes urgent calls harder to trust. Verification habits are now more important than voice recognition.

Device Code Phishing: Why MFA Can Still Be Bypassed: practical guidance, risks, checklist and next steps.

Backup Strategy For Small Teams: practical guidance, risks, checklist and next steps.

SaaS Security Checklist Before Buying A New Tool: practical guidance, risks, checklist and next steps.

Email Penetration Testing: Is It Worth It For Small Teams?: practical guidance, risks, checklist and next steps.
API Penetration Testing Explained For Non-Technical Founders: practical guidance, risks, checklist and next steps.

Domain Name Security: Registrar Locks, MFA And DNS Protection: practical guidance, risks, checklist and next steps.

Secure Hosting Checklist For WordPress Sites: practical guidance, risks, checklist and next steps.

Cyber Insurance For UK Small Businesses: practical guidance, risks, checklist and next steps.

Cyber Essentials: A Plain-English Guide For Small Businesses: practical guidance, risks, checklist and next steps.
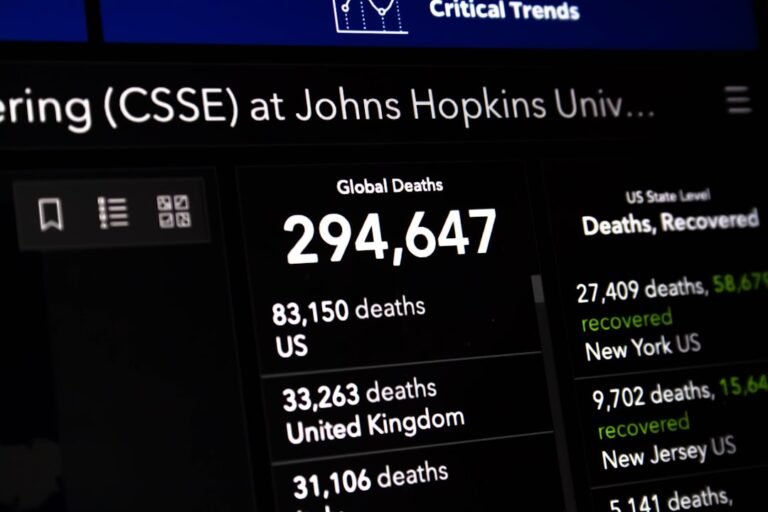
UK Cyber Security Breaches Survey 2025/2026: What Small Businesses Should Learn: practical guidance, risks, checklist and next steps.
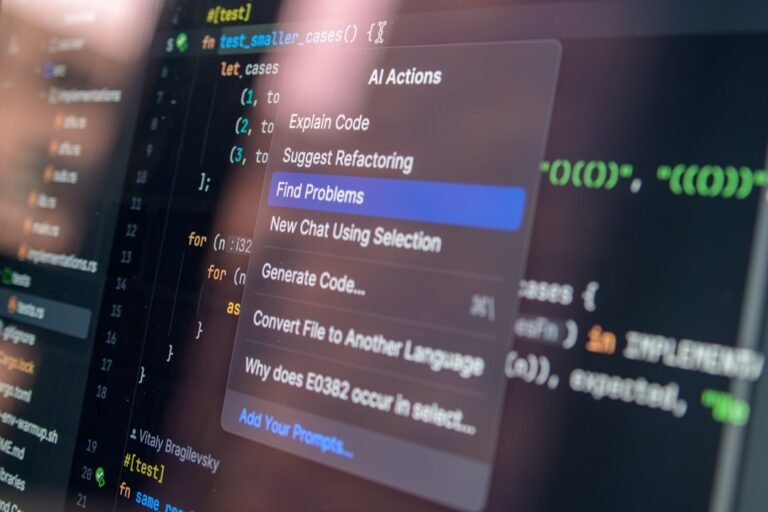
How To Review AI-Generated Code Before It Reaches Production: practical guidance, risks, checklist and next steps.

What Permissions Should An AI Agent Never Have?: practical guidance, risks, checklist and next steps.

AI Meeting Assistants: Privacy And Data Retention Risks: practical guidance, risks, checklist and next steps.

Shadow AI: How To Find The Tools Staff Are Already Using: practical guidance, risks, checklist and next steps.

MCP Security Explained: Why AI Tool Connectors Need Guardrails: practical guidance, risks, checklist and next steps.
Free PDF guide
A strategic guide to securing the intelligent enterprise: risks, governance and defence-in-depth for 2026.

Free PDF guide
Enter your email and we will unlock the PDF guide immediately.