Secure hosting matters because a WordPress site often holds brand trust, lead forms, customer enquiries and business-critical content. If you need the wider context, start with small business cybersecurity checklist. This guide focuses on hosting choices, backups, access control, updates and recovery for WordPress sites, with practical controls that a UK team can use before the next tool, supplier or incident forces the issue.
Cheap or unmanaged hosting can be fine for some sites, but owners need to understand backups, updates, access, malware response and support before something breaks. The answer is not panic and it is not blind adoption. The answer is a clear boundary: what is allowed, who owns it, what must be checked, and how the team will know if something goes wrong.
Why secure WordPress hosting matters now
Small businesses increasingly rely on websites for enquiries, bookings, lead magnets and paid campaigns. This is why the topic should sit in normal business planning rather than being treated as a side project. Security works best when the control is built into the workflow, not added after staff have already found their own shortcuts.
The most useful external reference for secure WordPress hosting is NCSC small business guide. Read it as a baseline, then compare it with the exact systems, data and decisions your team handles.
A website backup is only a backup if you know how quickly it can be restored.
The risk in plain English
The risk is that a simple website issue becomes downtime, spam, data exposure or lost leads because hosting controls were unclear. Most failures are not caused by one dramatic mistake. They are caused by small permissions, old assumptions and unclear review points connecting together. A safe process breaks that chain before one weak point becomes a business problem.
- No tested backups.
- Weak admin access.
- Outdated PHP or plugins.
- No malware response process.
- Poor DNS or domain security.
- Limited support during incidents.
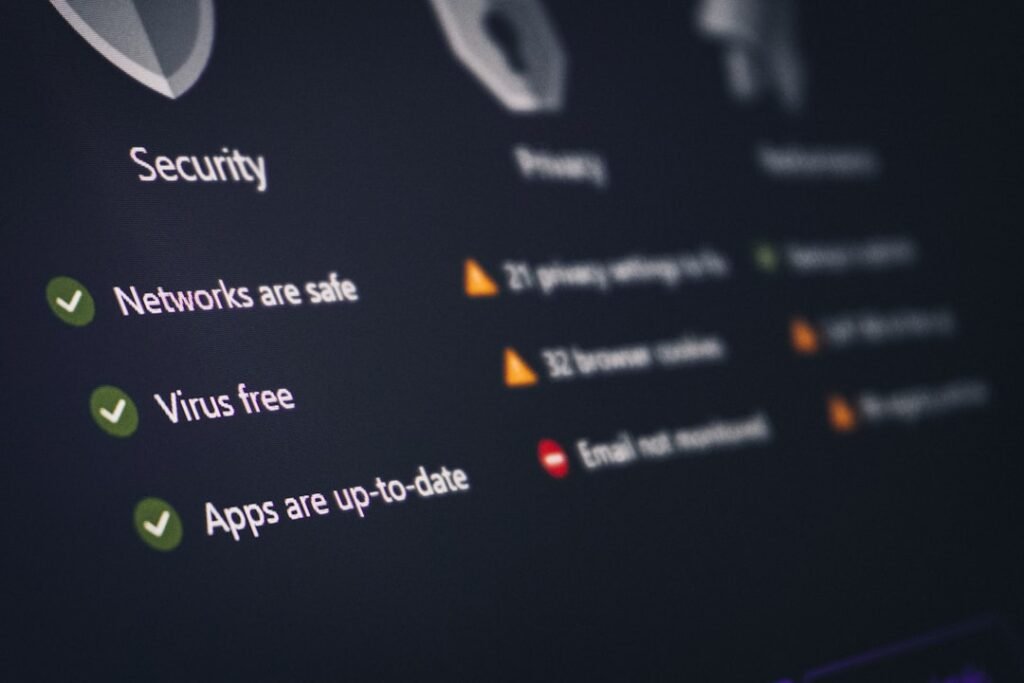
What good looks like
Good practice for secure WordPress hosting should be easy to recognise in daily work. People should know the rule, the owner should be able to show the setting or record, and the team should understand what to do if the control fails.
| Area | Weak setup | Safer setup |
|---|---|---|
| Backups | Exist but untested | Daily backups with restore checks |
| Access | Shared admin login | Named users and MFA |
| Support | Unclear response | Know escalation route |
A practical checklist
Use the checklist below as the first working version for secure WordPress hosting. Review it when the tool, supplier, workflow or risk level changes.
- Check backup frequency and retention.
- Enable MFA for hosting and WordPress admins.
- Use current PHP.
- Keep plugins minimal and updated.
- Secure domain registrar account.
- Know malware cleanup options.
How to roll this out without slowing the team down
For secure WordPress hosting, begin with the workflow where a mistake would hurt most. One completed improvement in that place is more useful than a broad plan that nobody owns.
- Name an owner for secure WordPress hosting.
- List the tools, accounts, data or workflows involved.
- Decide what is allowed, blocked and approval-only.
- Make the rule easy to find and easy to follow.
- Add a review date and a reporting route for problems.
- Update related posts, policies or checklists when the process changes.
Common mistakes
The mistakes below are common around secure WordPress hosting. They become easier to fix once the team knows who should notice them and what the next action should be.
- Choosing hosting only by price.
- Ignoring staging and restore features.
- Letting agencies keep sole access.
- Forgetting DNS and domain accounts.
Internal links and next steps
Hosting belongs in business security because downtime and compromise affect revenue, trust and incident response. For a broader control set, read cyber risk register guide and incident preparation guide. If the topic touches personal data, also connect it to personal data sharing and privacy basics.
Questions people usually ask
Is managed WordPress hosting always safer?
Not automatically, but good managed hosting can reduce update, backup and response burden.
What is the first hosting control?
Protect hosting, WordPress and domain registrar accounts with strong credentials and MFA.
How often should backups run?
It depends on update frequency, but business sites should usually have at least daily backups and tested restore paths.
Final recommendation
Choose hosting by recovery, access control and support quality, not only monthly price. Write down the rule, test it against a real example, and improve it after the first review. Good security is not a perfect document. It is a repeatable behaviour that survives busy days.
Ask hosting providers about recovery
Speed, storage and price matter, but recovery matters more during an incident. Ask how backups are restored, who can request restoration, how malware cleanup works and what support is available outside normal hours. The best hosting decision is often the one that shortens downtime.
A realistic workplace example
A WordPress site is used for lead generation, PDFs and contact forms. If hosting fails or malware appears, the business loses trust and enquiries. Secure hosting is therefore not only a technical choice; it is part of revenue protection.
What to monitor
Monitoring secure WordPress hosting should stay simple. Pick a few signals that reveal whether the control is being followed, ignored or stretched beyond its original purpose.
- Backup retention
- Admin access
- Plugin update process
- Malware response options
A 30-day improvement plan
Improve secure WordPress hosting in short cycles. Complete one action, record what changed, then use that evidence to decide the next step.
- Protect hosting with MFA
- Test a restore
- Remove unused plugins
- Document who can contact support
Why this should stay practical
The hosting decision should be judged by how quickly the site can be recovered, not only how cheaply it can run.
The strongest control for secure WordPress hosting is the one people can follow during normal work. If the safe route is clear, quick and visible, it is more likely to become the default.
Decision rules for this topic
For hosting, the buying decision should include recovery speed, account protection and support quality.
- Choose hosting based on recovery and support, not only price.
- Protect hosting and domain accounts with MFA.
- Test restoration before a website incident.
Who should be involved
The site owner, hosting administrator and any agency should agree who can restore, update and secure the site.
When to revisit the guidance
Revisit hosting after traffic growth, lead-generation changes, malware alerts, plugin changes or poor support experiences.
Hosting questions that reveal quality
Ask how restores work, how long malware response usually takes, whether staging is available, how PHP versions are managed and how support handles urgent security issues. A provider that can answer clearly is easier to trust during a stressful incident.
Also check account ownership. The business should have direct access to hosting, WordPress and domain accounts, even if an agency manages the technical work day to day.
For lead-generation sites, test the full recovery path after a restore: forms, email delivery, tracking, PDF downloads and admin access. A restored site that cannot capture leads properly is only partly recovered.