
Device Code Phishing: Why MFA Can Still Be Bypassed
Device Code Phishing: Why MFA Can Still Be Bypassed: practical guidance, risks, checklist and next steps.
SecurityBlogs
How to spot, avoid, and respond to phishing, fraud, social engineering, and online scams.

Device Code Phishing: Why MFA Can Still Be Bypassed: practical guidance, risks, checklist and next steps.

Email Penetration Testing: Is It Worth It For Small Teams?: practical guidance, risks, checklist and next steps.
QR codes are convenient, but they hide the destination. That makes them useful for scammers.

Romance scams are emotional manipulation, not foolishness. Knowing the signs can help families intervene earlier.
Invoice fraud targets process gaps. Small teams need simple payment rules that are followed every time.
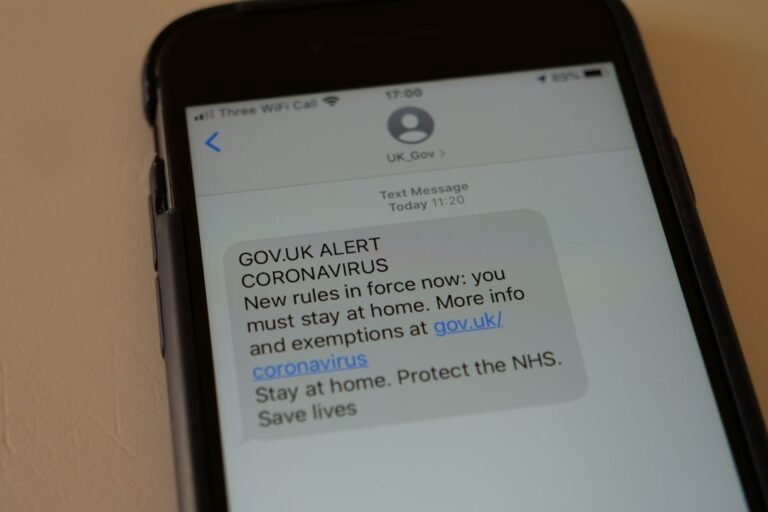
Parcel scam texts often use urgency and familiar delivery brands. A few checks can stop an expensive mistake.

Voice cloning makes urgent calls harder to trust. Verification habits are now more important than voice recognition.
A long-form guide to modern phishing emails, AI-written scams, warning signs, reporting routes and practical checks for UK…
Free PDF guide
A strategic guide to securing the intelligent enterprise: risks, governance and defence-in-depth for 2026.

Free PDF guide
Enter your email and we will unlock the PDF guide immediately.